Cellebrite

Upcoming Cellebrite Events

Date: Wednesday, May 27th
Time: 14:00 BST
Duration: 45 minutes (includes Q&A)
The investigation turns inward. The employee’s corporate devices are collected for forensic examination. They’re clean. No suspicious apps. No unusual transfers. The case nearly stalls.
Then someone remembers the security footage. The phone on the desk during those client meetings wasn’t the corporate phone. It was a personal device. And when forensic examiners get access to it, what they find is methodical, systematic, and far bigger than four victims.
The insider was not the mastermind. The insider was the supply chain. And what had already been done with the stolen identities changes everything.
You will walk away with:
- Why limiting forensic analysis to corporate devices can derail an insider threat investigation
- How mobile device extraction recovers recordings, images, and encrypted messaging data from personal devices
- Techniques for determining the full scope of an insider compromise through device timeline reconstruction
- Episode 3: The Digital Trail
- Don't miss out on the next episode! Click Here
- The Day Your Identity Disappeared
- Start from the beginning or catch up on the episodes you missed. Click Here
Date: Wednesday, June 10th
Time: 14:00 BST
Duration: 45 minutes (includes Q&A)
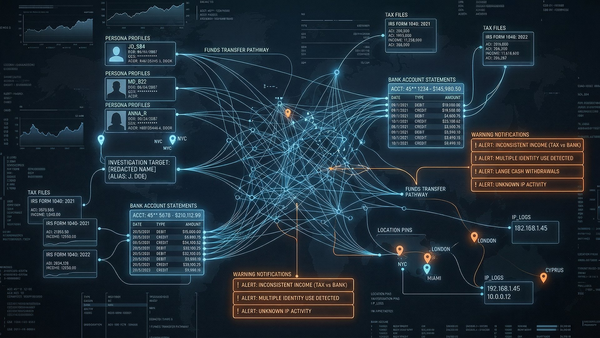
Fourteen accounts at different banks. All opened with stolen identities. All designed to look completely unrelated. But when investigators analyse the digital fingerprints behind the applications, connections emerge with shared IP addresses, matching device identifiers, email patterns that were never meant to be found.
The money trail reveals something even more sophisticated. Fake companies. Fake payrolls. Tax refunds claimed on income that was never earned. The stolen identities weren’t used to steal money. They were used to create it.
Then the device fingerprints match activity in two other regions. This was never about one bank.
You will walk away with:
- How entity resolution connects accounts and transactions deliberately designed to look unrelated
- Techniques for detecting financial structuring — transactions calibrated to avoid reporting thresholds
- How device fingerprint expansion uncovers connected criminal activity across jurisdictions
- Episode 4: The Network
- Be sure to catch the next episode! Click Here
- The Day Your Identity Disappeared
- Start from the beginning or catch up on the episodes you missed. Click Here
Date: Wednesday, June 24th
Time: 14:00 BST
Duration: 45 minutes (includes Q&A)
The final episode reveals the full picture. Three insiders at different institutions. A small group of operators building financial infrastructure from stolen identities. Money movers extracting funds across regions. Eighteen months of patient, methodical operation.
When investigators map the complete network for the first time, the structure of the criminal operation becomes visible in a way that no single case file could reveal. The question shifts from who did this to whether the evidence chain will hold up in court.
The series ends where every investigation ends: with the question of whether justice is served. And with a harder question for the audience — would your team have caught it?
You will walk away with:
- How network visualization reveals the structure of criminal operations hidden across institutions and regions
- The requirements for cross-jurisdictional evidence sharing that maintains chain of custody and legal admissibility
- A framework for evaluating your own institution’s readiness to detect and investigate complex financial crime
- See it in Action
- Want to see how these investigation techniques work for your team? Click Here
- The Day Your Identity Disappeared
- Start from the beginning or catch up on the episodes you missed. Click Here