
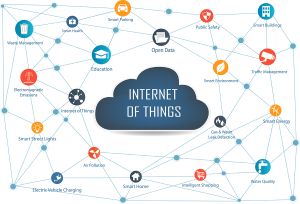
"Our world is more connected than ever." This phrase can be interpreted in many ways, one being the growth of Internet of Things (IoT) devices. Traditional materials and devices, including bridges, streetlights, water processing machines, home refrigerators, and even our doorbells, are now connected to the internet and to users who need to track how they are functioning. However, this cyber connection also means that these devices are open for others to access and use in ways we never envisioned.
Cybersecurity practices must now extend to non-cyber products to ensure that operational technology does not compromise information technology or the networks that connect them. In fact, 1.5 billion attacks were launched against IoT devices in a single year.
Efforts to secure IoT devices must happen across all levels of users, from the federal government through state and local agencies to even citizen consumers. Continue reading



 Digital twins
Digital twins With so many high-profile hacks this year, it's easy to want to throw up your hands and say, "Is there nothing that can be trusted?!" Interestingly, that lament is what is driving the latest approach to cybersecurity -- zero trust. Zero trust is what it sounds like, a security approach
With so many high-profile hacks this year, it's easy to want to throw up your hands and say, "Is there nothing that can be trusted?!" Interestingly, that lament is what is driving the latest approach to cybersecurity -- zero trust. Zero trust is what it sounds like, a security approach 
